Features
Das Multi-Talent für herstellerunabhängige Netzwerk-Discovery, Network Visibility & Management von IT-Infrastrukturen
Network Monitoring
Einfache Überwachung von: Geräte-spezifisch z.B. Verfügbarkeiten, CPU-Auslastung, Stromversorgung, Port-spezifischer Bandbreitenauslastung
Konfiguration Management
Das Konfigurationsmanagement ermöglicht die Sicherung der aktuellen Konfigurationen aller Netzwerkgeräte
WLAN Topology
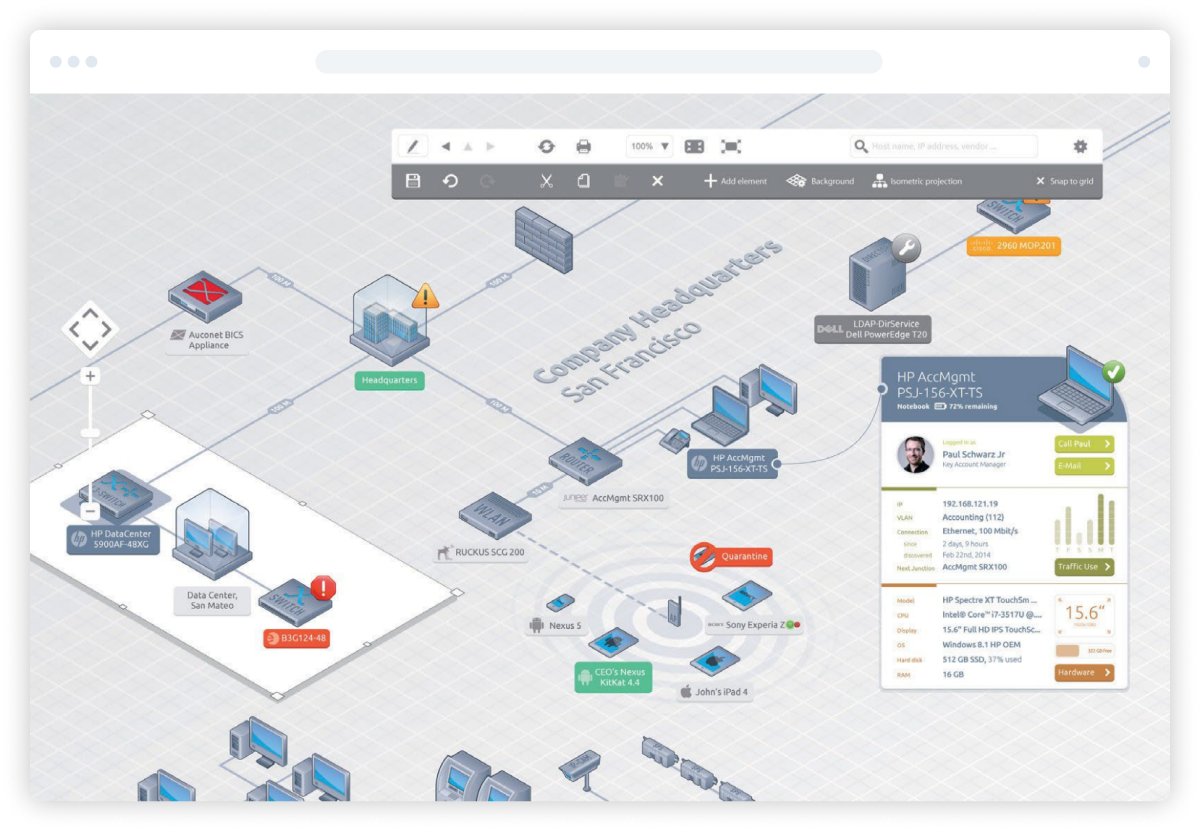
Grafische Darstellung der Access Points und benachbarter Switche und WLAN Controller sowie der Übergänge von drahtloser zu drahtgebundener Kommunikation.
Real View Device Details
Spezielle, Gerätetyp-spezifische Sichten auf individuelle Geräteparameter.
Syslog Analyzer
Auswertung von Meldungen von Netzwerkgeräten, die im Syslog-Format gesendet wurden.
VLAN Management
Generische, herstellerübergreifende Funktionen zum Administrieren von VLANs auf Netzwerkgeräten.
Produkte
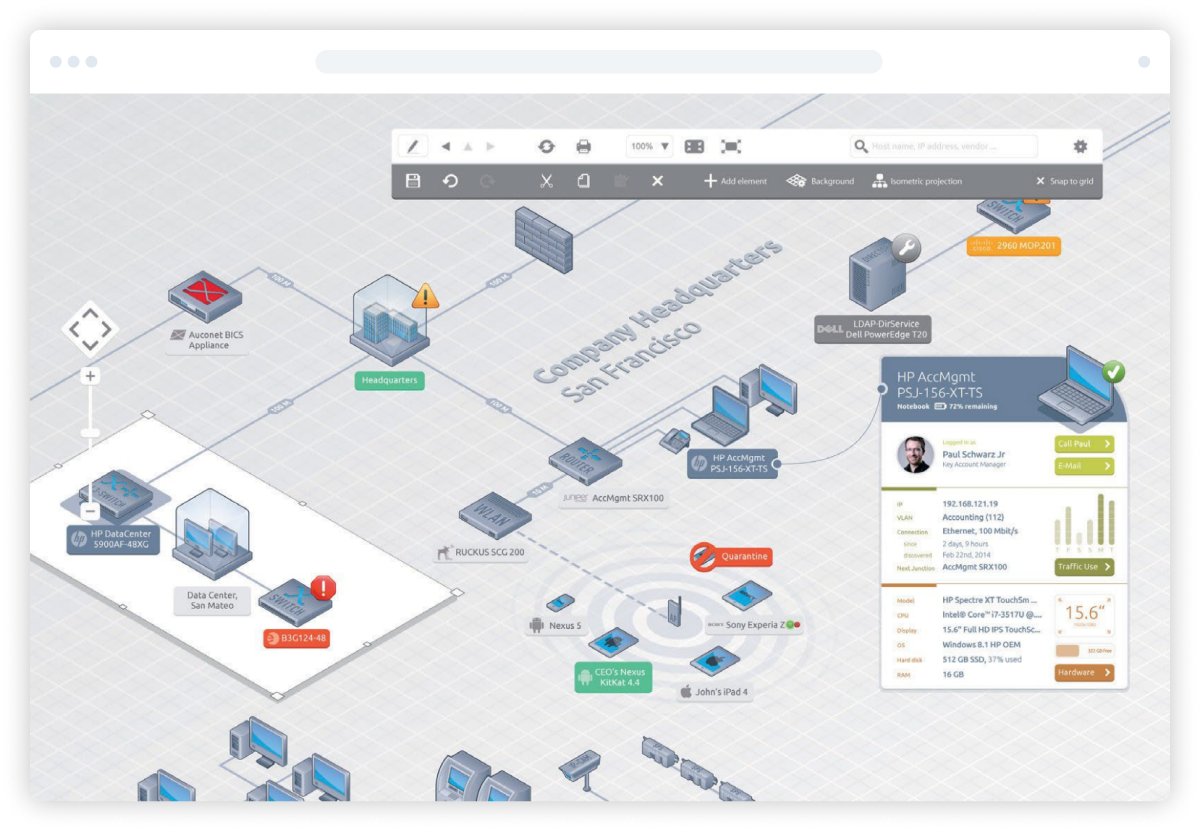
Netzwerk Discovery & Visibility
Unser Netzwerk Management bietet leistungsstarke Möglichkeiten, ein IT-Netzwerk zu verwalten, die Performance sicherzustellen und die Verfügbarkeit und Funktionalität der einzelnen Netzwerkkomponenten zu überwachen.
Visualisiert die gesamte Netzwerk-Topologie
Bis zu 90% weniger Zeitaufwand
Alles in einem Dashboard
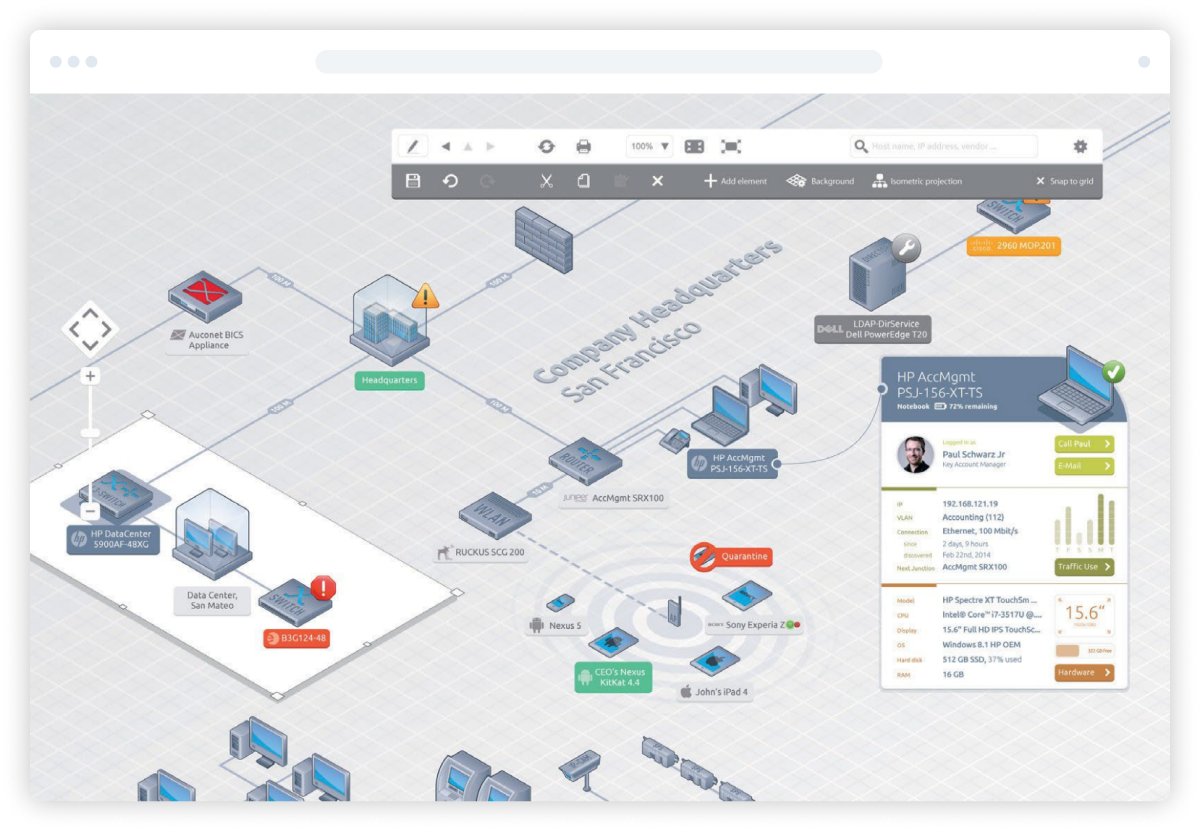
Netzwerk Management & Monitoring
Unser Netzwerk Management bietet leistungsstarke Möglichkeiten, ein IT-Netzwerk zu verwalten, die Performance sicherzustellen und die Verfügbarkeit und Funktionalität der einzelnen Netzwerkkomponenten zu überwachen.
Visualisiert die gesamte Netzwerk-Topologie
Bis zu 90% weniger Zeitaufwand
Alles in einem Dashboard
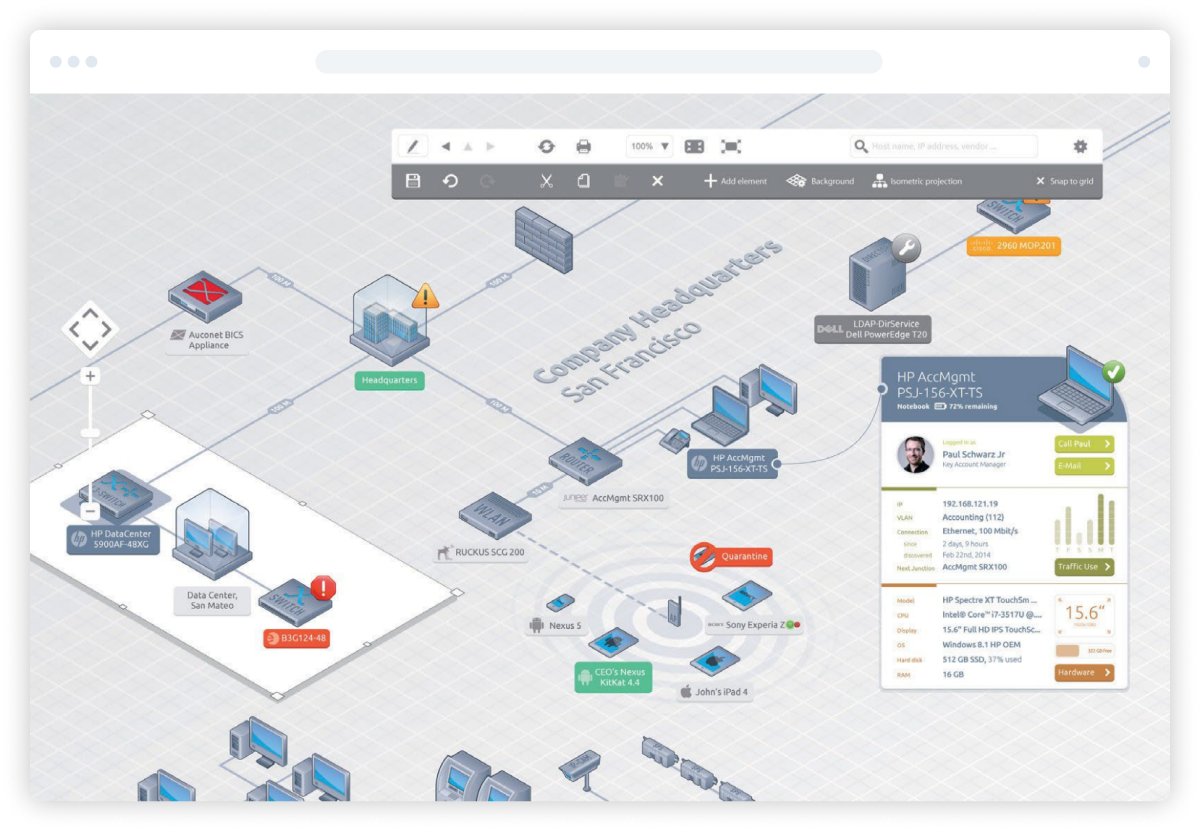
Netzwerk Security
Unser Netzwerk Management bietet leistungsstarke Möglichkeiten, ein IT-Netzwerk zu verwalten, die Performance sicherzustellen und die Verfügbarkeit und Funktionalität der einzelnen Netzwerkkomponenten zu überwachen.
Visualisiert die gesamte Netzwerk-Topologie
Bis zu 90% weniger Zeitaufwand
Alles in einem Dashboard
Asset Management
Unser Netzwerk Management bietet leistungsstarke Möglichkeiten, ein IT-Netzwerk zu verwalten, die Performance sicherzustellen und die Verfügbarkeit und Funktionalität der einzelnen Netzwerkkomponenten zu überwachen.
Visualisiert die gesamte Netzwerk-Topologie
Bis zu 90% weniger Zeitaufwand
Alles in einem Dashboard
System Management
Unser Netzwerk Management bietet leistungsstarke Möglichkeiten, ein IT-Netzwerk zu verwalten, die Performance sicherzustellen und die Verfügbarkeit und Funktionalität der einzelnen Netzwerkkomponenten zu überwachen.
Visualisiert die gesamte Netzwerk-Topologie
Bis zu 90% weniger Zeitaufwand
Alles in einem Dashboard
Über uns
Netzwerkmanagement seit 1998 - made in Germany.
Infraray wurde 1998 von einem deutschen Ingenieurteam mit langjähriger Erfahrung im Bereich IT Operations Management gegründet. Das Unternehmen bietet Lösungen für Netzwerkmanagement, Netzwerksicherheit, IT-Infrastrukturmanagement, Netzwerkautomatisierung und die Steuerung der kompletten Geschäftsinfrastruktur.
Seit Anfang 2018 ist Infraray Teil der Beta Systems Group.
Lösungen
Eine Lösung für alle Rollen und Zuständigkeiten in Ihrer IT-Abteilung

IT-Administration
Sie suchen für Ihre Arbeitsumgebung eine umfassende Netzwerkmanagement-Lösung?
Наслаждайтесь азартными играми на деньги онлайн на сайте X-Casino. Огромный выбор азартных развлечений доступен на официальном сайте ресурса. Рулетка, покер, блэкджек, баккара, бинго, маджонг, кено, крэпс, игровые автоматы на любую тематику. Каждый найдёт здесь что-то для себя. Начните играть в азартные игры уже сегодня на гемблерском портале X-Casino.

Teamleitung
Sie suchen nach einer umfassenden Lösung für Ihre Netzwerkumgebung & die Ihres Teams?
Большие бонусы доступны новым пользователям в азартном клубе Vavada casino. Если зарегистрироваться на официальном сайте ресурса, то можно получить приветсвенное предложение – бездепозитный бонус +100 фриспинов на все слоты азартного клуба. Выигрывайте джекпоты онлайн, не выходя из собственного дома с бонусами азартного сервиса Vavada casino.

Geschäftsleitung
Sie sind Manager und wollen Kosten sparen & dabei Ihre Netzwerkumgebung ausbauen?
Сайт азартных игр Cat Casino – популярный клуб для гемблинга в интернете. Если портал оказался недоступен, то вы всегда можете использовать рабочее зеркало азартного клуба. Также есть возможность играть на деньги со своего мобильного девайса. Cat Casino – всегда доступный азартный портал.

Wissensvorsprung dank unserer Whitepaper
Entdecken Sie unser umfangreiches Angebot an Whitepapern, die Ihnen einen wertvollen Wissensvorsprung verschaffen werden! In unseren kostenlosen Whitepapern finden Sie fundierte Informationen und praktische Tipps zu den neuesten Technologien, Trends und Best Practices in verschiedenen Branchen und Fachgebieten.

„Unsere Infraray-Infrastrukturkontrolle erhöht unsere Sicherheit, senkt unsere Servicekosten drastisch und bringt unsere Maschinen schneller wieder in Betrieb, in vielen Fällen ohne Bedienereingriff!“
Michael Böttcher · IT Security Engineer · Water Supply Control System, Berliner Wasserbetriebe